
Today, the FBI, CISA, and the Department of Health and Human Services (HHS) warned U.S. healthcare organizations of targeted ALPHV/Blackcat ransomware attacks.
"ALPHV Blackcat affiliates have been observed primarily targeting the healthcare sector," the joint advisory cautions.
Today's warning follows an April 2022 FBI flash alert and another advisory issued in December 2023 detailing the BlackCat cybercrime gang's activity since it surfaced in November 2021 as a suspected rebrand of the DarkSide and BlackMatter ransomware groups.
The FBI linked BlackCat to over 60 breaches during its first four months of activity (between November 2021 and March 2022) and said the gang has raked in at least $300 million in ransoms from over 1,000 victims until September 2023.
"Since mid-December 2023, of the nearly 70 leaked victims, the healthcare sector has been the most commonly victimized," the three federal agencies warned in today's joint advisory.
"This is likely in response to the ALPHV Blackcat administrator's post encouraging its affiliates to target hospitals after operational action against the group and its infrastructure in early December 2023."
The FBI, CISA, and HHS advised critical infrastructure organizations to take necessary mitigation measures to minimize the likelihood and impact of Blackcat ransomware and data extortion incidents.
Moreover, they've urged healthcare organizations to implement cybersecurity safeguards to counteract prevalent tactics, techniques, and procedures commonly employed within the Healthcare and Public Health (HPH) sector.
BlackCat now using ScreenConnect for initial access
Today's advisory comes after the BlackCat ransomware operation was linked to a cyberattack on UnitedHealth Group subsidiary Optum that triggered an ongoing outage impacting Change Healthcare, the largest payment exchange platform connecting doctors, pharmacies, healthcare providers, and patients in the U.S. healthcare system.
While UnitedHealth Group VP Tyler Mason did not confirm the BlackCat link in a statement shared with BleepingComputer, he said that 90% of the 70,000+ pharmacies using the impacted platform have switched to new electronic claim processes.
Sources familiar with the investigation told BleepingComputer that Change Healthcare has been conducting Zoom calls with partners in the healthcare industry to provide updates since the attack hit its systems.
BleepingComputer learned the attack had been linked to the BlackCat ransomware group by forensic experts investigating the incident and that the threat actors breached the network using the actively exploited critical ScreenConnect auth bypass vulnerability (CVE-2024-1709).
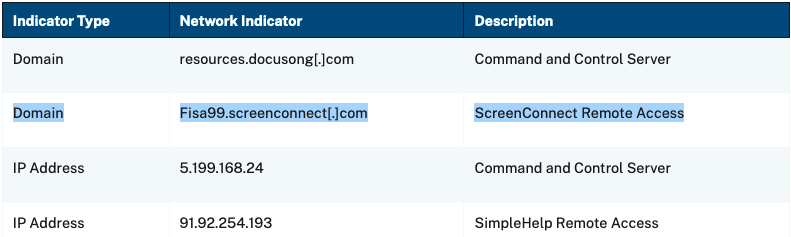
Even though the FBI, CISA, and the HHS didn’t link today’s advisory to the Change Healthcare incident, they shared indicators of compromise that confirm our reporting that the BlackCat ransomware gang is targeting vulnerable ScreenConnect servers for remote access into victim networks.
The FBI disrupted the BlackCat gang's operations in December by taking down its Tor negotiation and leak sites. The gang's servers were also hacked, which allowed law enforcement to create a decryptor using collected keys during a months-long intrusion.
BlackCat has since "unseized" their sites and switched to a new Tor leak site that the FBI has not yet taken down.
The U.S. State Department offers rewards of up to $10 million for details leading to the identification or location of BlackCat gang leaders and $5 million for tips on individuals linked to the group's ransomware attacks.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now