
A premium WordPress plugin named LayerSlider, used in over one million sites, is vulnerable to unauthenticated SQL injection, requiring admins to prioritize applying security updates for the plugin.
LayerSlider is a versatile tool for creating responsive sliders, image galleries, and animations on WordPress sites, allowing users to build visually appealing elements with dynamic content on online platforms.
Researcher AmrAwad discovered the critical (CVSS score: 9.8) flaw, tracked as CVE-2024-2879, on March 25, 2024, and reported it to WordPress security firm Wordfence via its bug bounty program. For his responsible reporting, AmrAwad received a bounty of $5,500.
The flaw, which impacts versions 7.9.11 through 7.10.0 of the plugin, could allow attackers to extract sensitive data, such as password hashes, from the site's database, putting them at risk of complete takeover or data breaches.
Technical details provided in Wordfence's report reveal that the vulnerability existed within the plugin's 'ls_get_popup_markup' function's handling of the 'id' parameter.
This function fails to sanitize the 'id' parameter properly, allowing attackers to inject malicious SQL code into specially crafted queries, resulting in command execution.
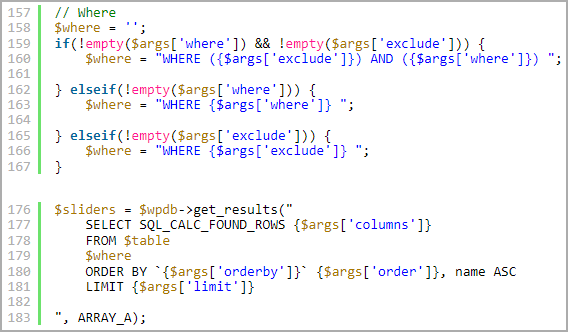
The structure of the possible queries limits the attack to time-based blind SQL injection, meaning that the attackers need to observe the response times to infer data from the database.
Despite this limitation, CVE-2024-2879 still enables malicious actors to extract information from the site's database without requiring any authentication on the site, including password hashes and sensitive user information.
Wordfence explains that the issue is further exacerbated because the queries are not prepared using WordPress's '$wpdb->prepare()' function, which prevents SQL injection by ensuring that user input is sanitized before being used in database queries.
The plugin's creator, Kreatura Team, was immediately notified of the flaw and quickly acknowledged the report. The developers released a security update on March 27, 2024, less than 48 hours after initial contact.
All users of LayerSlider are recommended to upgrade to version 7.10.1, which addresses the critical vulnerability.
In general, it is important for WordPress site admins to keep all their plugins up to date, disable those that aren't needed, use strong account passwords, and deactivate dormant accounts that can be hijacked.


Comments
fromFirefoxToVivaldi - 3 weeks ago
Like I said before, it would be great if WordPress took over in such cases. The moment a vulnerability is found, automatic plugin upgraded should be enforced, because the ones truly at risk are not the website owners, but people who simply visit a website.
This is why WordPress shouldn't care about potential compatibility issues. The safety of people visiting a random website is more important than said random website breaking due to an upgrade.
The mechanism exists, just google "Millions of WordPress sites get forced update to patch critical plugin flaw". I wish it would be used every single time a vulnerability is found in a plugin.
Otto42 - 2 weeks ago
This a premium plugin which means that it's not free, which means that it is not on WordPress at all.
Therefore, we do not control updates for it or any way have any say over what he does. This is the cost of using non-free plugins. You are subject to their rules, not ours.
fromFirefoxToVivaldi - 2 weeks ago
This is a plugin which shows up on the available updates list and can be updated straight from there. Would it not be possible to try to apply an update and just move on if that fails due to a lack of a valid license?
Even disregarding premium plugins, what about cases like the one from March, when an old vulnerable Popup Builder was exploited, despite the vulnerability having been patched in November (vide "Hackers exploit WordPress plugin flaw to infect 3,300 sites with malware")?