
Ransomware continues to hit organizations in all sectors, and attacks regularly make media headlines because of their hard-hitting impact on affected parties. The earliest example of ransomware stretches back to 1989, but its success during the last decade saw it becoming arguably the most lucrative form of cyber attack.
Most recently, Change Healthcare – the country’s largest healthcare payment processor – fell victim to a major ransomware attack. The effects of the attack are still coming to light, aside from the nearly 70,000 pharmacies directly impacted by the attack.
Here’s a lowdown on some recent ransomware attacks, lessons worth learning from them, and tips to help limit ransomware risk.
Recent Ransomware Attacks
Veolia North America
Veolia North America is a water services company with an estimated $3 billion in annual revenue. However, the company’s high earning power couldn’t stop a January 2024 ransomware attack that hit back-end software applications and systems. The back-end system outages caused delays to the company’s bill portal, but luckily no water treatment operations were hit.
Lessons:
-
Prompt action from the incident response team prevented the attack from escalating to hit operational technology systems.
-
Ransomware gangs don’t only hit traditional businesses; they also hunt out big targets like critical infrastructure operators.
VF Corporation
VF Corporation is the parent company behind well-known consumer brands like Vans and The North Face. A December 2023 ransomware attack against VF involved data exfiltration (a double extortion incident). The hackers managed to steal the personal information of 35 million customers. Also, the need to shut down some systems resulted in canceled customer orders and delays in shipments.
Lessons:
-
Ransomware attacks have knock-on financial impacts when companies need to swiftly shut down systems that might form the backbone of their normal operations.
-
Personal data is a potential goldmine for money-hungry ransomware gangs looking to increase their paydays.
What Organizations Can Do to Limit Ransomware Risk
With the onslaught of ransomware attacks companies face and the ever-evolving tactics deployed by hackers, reducing your risks against this nefarious cyber threat calls for multiple layers of defense.
Here are some of the key areas worth considering.
Email Security
Ransomware attacks involve multiple phases. Initial access to company networks often starts from an employee unknowingly clicking on a shady link or downloading a malicious attachment. In fact, recent research found that malicious emails are the third most common initial attack vectors in ransomware campaigns.
Effective email security helps to reduce the chances of successful ransomware attacks by preventing malicious emails from reaching employee inboxes. Consider email security solutions that filter incoming emails to detect phishing attempts, malicious attachments, and links using machine learning algorithms, natural language processing, and other advanced technologies.
Endpoint Security
It’s not just about trying to stop phishing, though. There are layers to ransomware mitigation on end-user devices like workstations and laptops. Ransomware gangs often target endpoints as gateways into your broader network.
Compromising a single device can allow attackers to move laterally across the network, elevate privileges, and eventually install ransomware strains on the entire suite of IT systems.
Endpoint security solutions go beyond traditional antivirus software by incorporating firewalls, intrusion prevention systems, and advanced threat detection capabilities to identify and block ransomware before it executes on a user’s device. Endpoint tools also identify suspicious activities indicative of ransomware, such as rapid file encryption, and neutralize the threat by isolating devices.
It’s important to look for areas within your endpoint security processes to improve. For instance, identify how quickly your team responds with isolating devices.
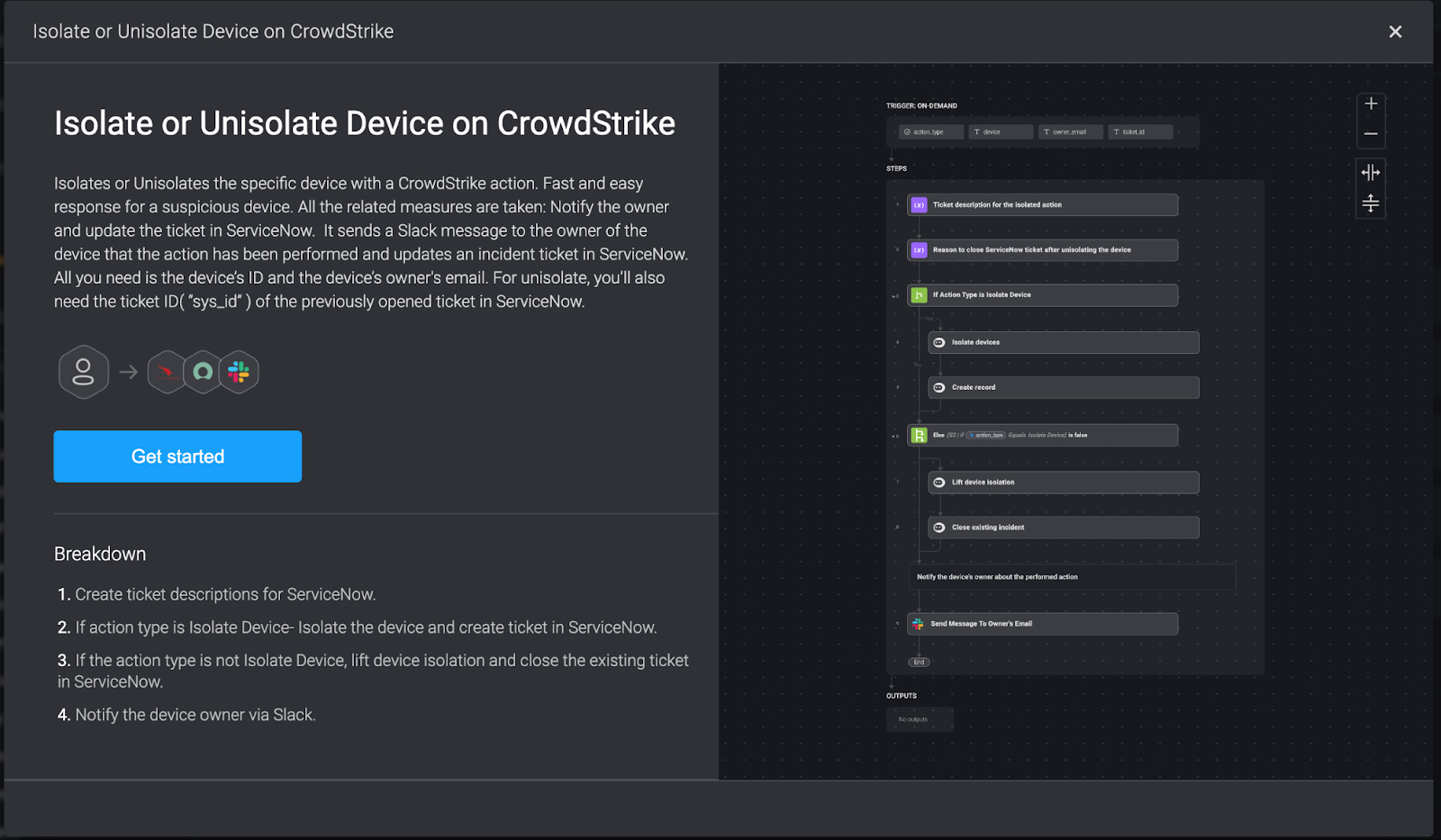
With a security automation copilot like Blink, isolating or unisolating a device on Crowdstrike is easy. The pre-built workflow below can start automating in seconds.
Properly Encrypt Sensitive Data
One of the defining shifts in ransomware gangs’ operations over the last few years is becoming more data-focused. The emergence of the double extortion attack saw threat actors exfiltrating sensitive data in addition to encrypting files and systems with ransomware strains.
This double whammy intends to put more pressure on organizations to pay up, and it’s a strategy that regularly bears fruit.
Encrypting sensitive data both at rest and in transit protects it from unauthorized access. Even if smart hackers get inside your network and access sensitive data stores or flows, the data remains unintelligible without the right decryption keys. Using strong encryption standards makes it practically impossible to crack the code and access your data.
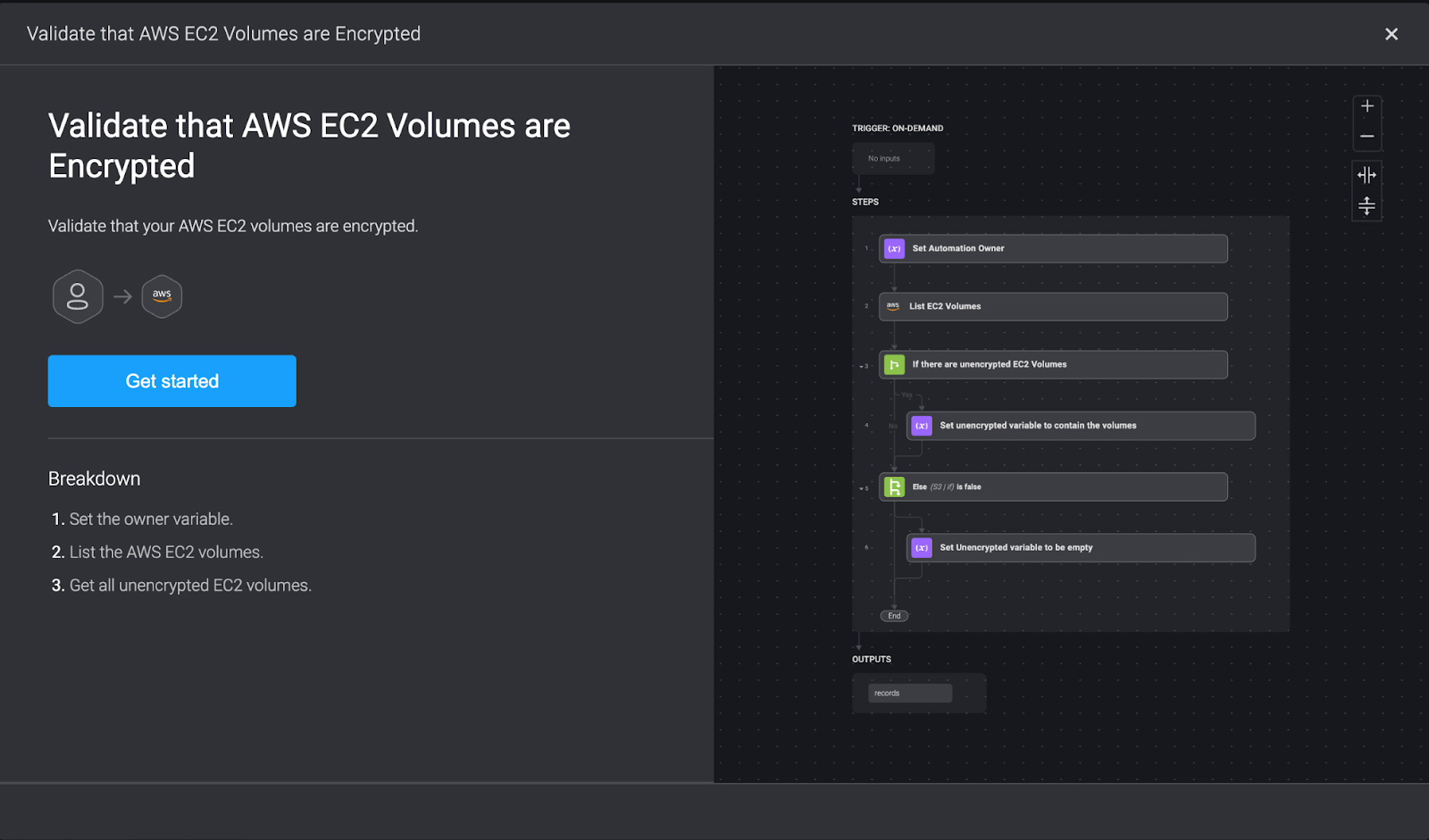
It’s worth noting that manually validating that your sensitive data is encrypted can be rather time-consuming. Automating repetitive tasks can ensure your encryption processes are operational. For instance, you could automate a workflow that validates that AWS EC2 volumes are encrypted.
Have a Solid Backup Strategy
While encrypting important files prevents ransomware gangs from blackmailing you with the threat of publishing sensitive data, you’ll likely still want access to those files. The problem is that ransomware strains will often block this access with their own encryption algorithms.
This is where a solid backup strategy comes into play. Maintain regular, encrypted backups of critical data and store them somewhere that’s not accessible from your main network. Test the backups to ensure they work and that you can restore important files quickly.
Patch Management
Exploiting vulnerabilities in public-facing apps was the number one way ransomware gangs gained initial network access in 2022. These vulnerabilities can range from outdated web servers to content management system (CMS) flaws to weaknesses in remote access services like remote desktop protocol.
Proper patch management protects against this threat by public-facing applications and systems. timely application of patches is essential in defending against these threats. It not only prevents ransomware attacks but also protects against a wide range of cybersecurity threats that exploit software vulnerabilities.
How Automation Reduces Ransomware Risks
By automating security tasks and developing smart workflows, you can better secure your environment against common ransomware entry points. Automation also facilitates rapid response to detected ransomware attacks.
Ransomware-focused automated workflows can scan files for malware and detonate them in a safe sandbox environment, deploy countermeasures instantly, verify employees have installed important tools like EDR systems on their devices, and perform other tasks much more efficiently than with manual efforts.
Whether it’s encrypting sensitive data or patching vulnerabilities, Blink enables you to start automating without the need to code. See it in action and schedule a demo today.
Sponsored and written by Blink Ops.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now