
Image: Midjourney
Microsoft says an Iranian-backed threat group has targeted thousands of organizations in the U.S. and worldwide in password spray attacks since February 2023.
The state hackers also stole sensitive information from a limited number of victims in the defense, satellite, and pharmaceutical sectors.
Tracked as APT33 (aka Peach Sandstorm, HOLMIUM, or Refined Kitten), the cyber-espionage group has been active since at least 2013, attacking entities from various industry verticals (including government, defense, research, finance, and engineering) in the United States, Saudi Arabia, and South Korea.
"Between February and July 2023, Peach Sandstorm carried out a wave of password spray attacks attempting to authenticate to thousands of environments," the Microsoft Threat Intelligence team said.
"Throughout 2023, Peach Sandstorm has consistently demonstrated interest in US and other country's organizations in the satellite, defense, and to a lesser extent, pharmaceutical sectors," Microsoft's Sherrod DeGrippo Threat Intelligence Strategy Director told BleepingComputer.
In password spray attacks, threat actors try to log in to many accounts using a single password or a list of commonly employed passwords.
This tactic differs from brute force attacks, where a single account is targeted with a long list of passwords. Password spraying enables attackers to significantly increase their chances of success while reducing the risk of triggering automatic account lockouts.
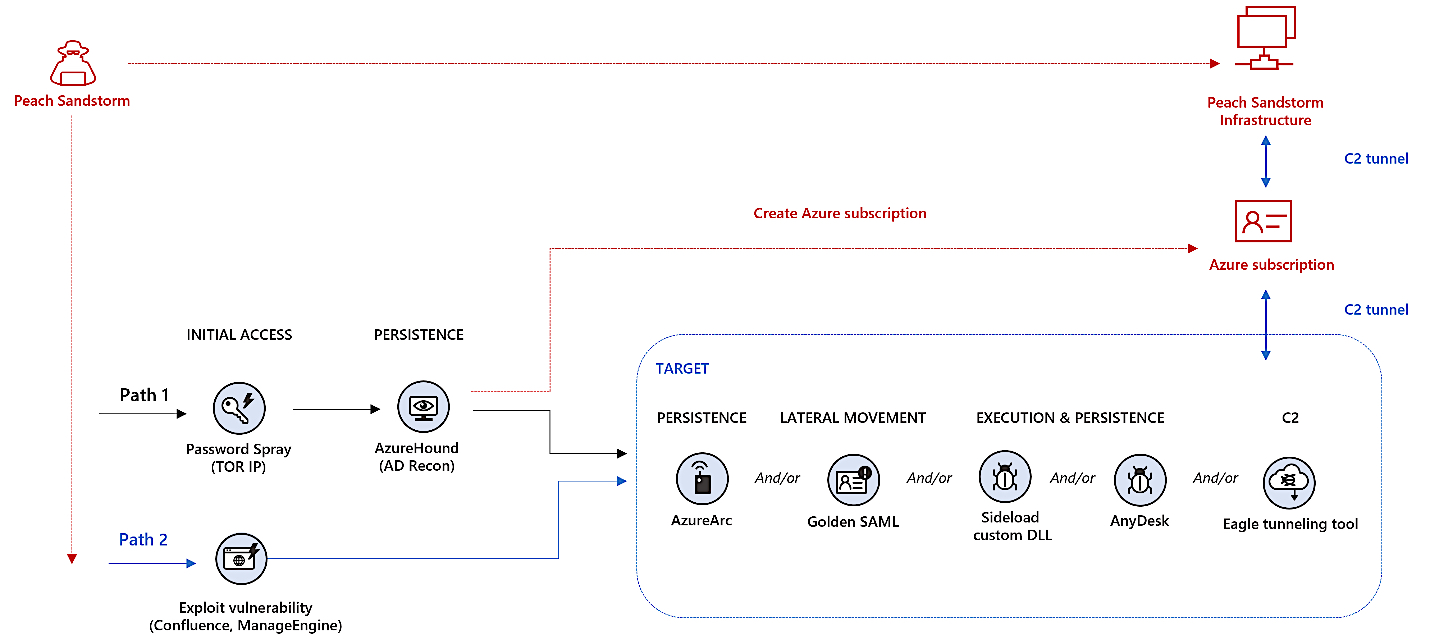
In contrast to noisy password spraying, the attackers also used exploits targeting unpatched Confluence and ManageEngine appliances exposed online to breach the targets’ networks.
Following successful attempts, the APT33 hackers used the AzureHound or Roadtools open-source security frameworks for reconnaissance across the victims' Azure Active Directory and to harvest data from their cloud environments.
They also used compromised Azure credentials, created new Azure subscriptions on the victims' tenants, or abused Azure Arc for persistence purposes to control on-premises devices within the victims' network.
The APT33 actors were also observed using Golden SAML attack techniques for lateral movement, deploying AnyDesk for persistence, sideloading custom malicious DLLs to execute malicious payloads, and employing a tunneling tool known as EagleRelay to tunnel malicious traffic to their command-and-control (C2) infrastructure.
"Based upon the profile of victim organizations targeted and the observed follow-on intrusion activity, Microsoft assesses that this initial access campaign is likely used to facilitate intelligence collection in support of Iranian state interests," Redmond said.
"Many of the cloud-based tactics, techniques, and procedures (TTPs) seen in these most recent campaigns are materially more sophisticated than capabilities used by Peach Sandstorm in the past," the company added.
As Microsoft's Identity Security Director, Alex Weinert, said three years ago, password spray attacks are among the most popular authentication attacks, amounting to more than a third of enterprise account compromises.
In July 2021, the NSA said the Russian APT28 military hacking group targeted the U.S. government and Department of Defense agencies in password spray attacks launched from Kubernetes clusters.
Months later, in October 2021, Microsoft also spotted the Iran-linked DEV-0343 and the Russian-sponsored Nobelium groups breaching defense tech companies and managed service providers (MSPs) in password spray attacks.


Comments
alexandresantosal91 - 7 months ago
Parabéns pelo excelente artigo sobre "Iranian hackers breach defense orgs in password spray attacks". É um artigo essencial para quem deseja entender um pouco mais sobre o mundo da cibersegurança e o nível de sofisticação dos ataques cibernéticos. O artigo é claro e fácil de entender, e os exemplos são bem escolhidos. Achei especialmente interessante a sua abordagem sobre como os hackers iranianos usam listas de senhas comprometidas para aumentar suas chances de sucesso.
alexandresantosal91 - 7 months ago
Congratulations on the excellent article on "Iranian Hackers Breach Defense Organizations in Password Spray Attacks". It is an essential article for anyone who wants to understand a little more about the world of cybersecurity and the level of sophistication of cyber attacks. The article is clear and easy to understand, and the examples are well chosen. I found your take on how Iranian hackers use lists of compromised passwords to increase their chances of success especially interesting.