
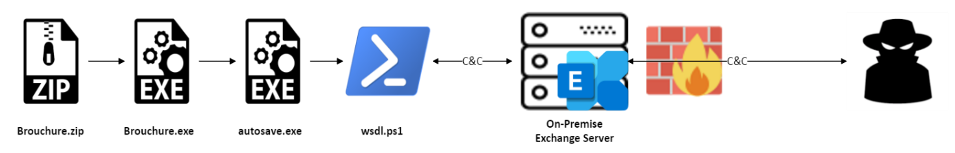
A new PowerShell-based malware dubbed PowerExchange was used in attacks linked to APT34 Iranian state hackers to backdoor on-premise Microsoft Exchange servers.
After infiltrating the mail server via a phishing email containing an archived malicious executable, the threat actors deployed a web shell named ExchangeLeech (first observed by the Digital14 Incident Response team in 2020) that can steal user credentials.
The FortiGuard Labs Threat Research team found the PowerExchange backdoor on the compromised systems of a United Arab Emirates government organization.
PowerExchange communicates with its command-and-control (C2) server via emails sent using the Exchange Web Services (EWS) API, sending stolen info and receiving base64-encoded commands through text attachments to emails with the "Update Microsoft Edge" subject.
"Using the victim's Exchange server for the C2 channel allows the backdoor to blend in with benign traffic, thereby ensuring that the threat actor can easily avoid nearly all network-based detections and remediations inside and outside the target organization's infrastructure," the FortiGuard Labs Threat Research team said.
The backdoor enables its operators to execute commands to deliver additional malicious payloads on the hacked servers and to exfiltrate harvested files.
During the forensic investigation of the network, the researchers also discovered additional backdoored endpoints with various other malicious implants.
Among them, they found the ExchangeLeech web shell, installed as a file named System.Web.ServiceAuthentication.dll that mimicked legitimate IIS file naming conventions.
ExchangeLeech collects the usernames and passwords of those logging into the compromised Exchange servers using basic authentication by monitoring clear text HTTP traffic and capturing the credentials from the webform data or HTTP headers.
The attackers can instruct the web shell to send the credential log via cookie parameters.
FortiGuard Labs linked these attacks to the Iranian state-backed hacking group APT34 (aka Oilrig) based on similarities between PowerExchange and the TriFive malware they used to backdoor the servers of Kuweiti government organizations.
"Both backdoors share striking commonalities: they are written in PowerShell, activated by a periodic scheduled task, and the C2 channel leverages the organization's Exchange server with EWS API. And while their code is much different, we speculate that PowerExchange is a new and improved form of TriFive," the researchers said.
APT34 also uses phishing emails as an initial infection vector in their attacks and has previously breached other UAE entities, according to Fortiguard Labs' report.


Comments
Mahhn - 10 months ago
Is there a CVE for this? Indicators Of Compromise? Mitigation?
serghei - 10 months ago
No CVE for malware, IOCs in the linked blog post at https://www.fortinet.com/blog/threat-research/operation-total-exchange-backdoor-discovered
Mahhn - 10 months ago
Thanks, that link is down, maybe doing an update or info changed.
I meant cve for the exchange server being exploited like that.
limelightwonderer - 10 months ago
The article with IOCs can be found here:
http://web.archive.org/web/20230525172132/http://www.fortinet.com/blog/threat-research/operation-total-exchange-backdoor-discovered