
A threat actor named Savvy Seahorse is abusing CNAME DNS records Domain Name System to create a traffic distribution system that powers financial scam campaigns.
The threat actor targets victims through Facebook ads that direct them to fake investment platforms where they're tricked into depositing funds and entering sensitive personal data.
A notable aspect of these campaigns is that they involve chatbots that directly interact with the victims to convince them of high investment returns, automating the scamming process for the attackers.
Infoblox researchers who discovered this operation say it has been underway since at least August 2021, manifesting in short attack waves that last between five and ten days.
Using DNS CNAME records as a TDS
Savvy Seahorse creatively uses Canonical Name (CNAME) records as a Traffic Distribution System (TDS) for its operations, allowing threat actors to easily manage changes, such as performing IP rotation that enhances detection evasion.
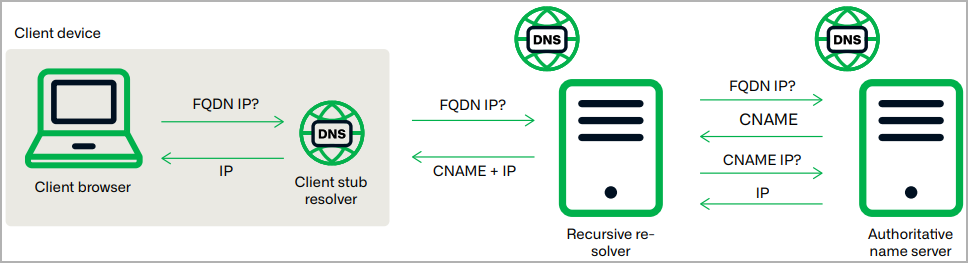
A CNAME record is a DNS record that maps a domain or subdomain to another domain name instead of directly to an IP address.
This causes the CNAME to act as an alias for the target domain, making it easier to manage redirects and ensure that any changes to the target domain's IP address automatically apply to the CNAME as well.
Savvy Seahorse registers multiple subdomains for its attack waves that share a common CNAME record linking it to primary/base campaign domain, for example, "b36cname[.]site."
This allows all of these CNAME records to have the same IP address inherited from the subdomain on the b36cname[.]site, as illustrated below.
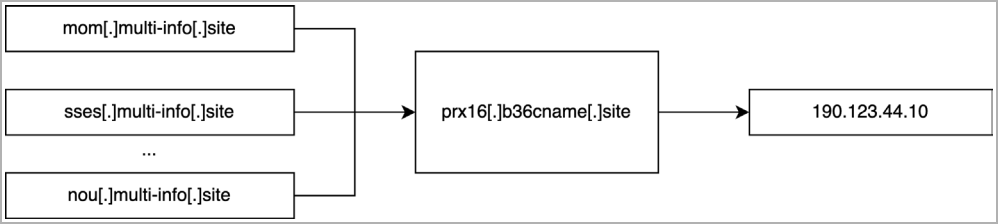
This technique makes it possible to rotate to new destinations when security software blocks a particular IP address or to prevent detection without altering the attack domain's DNS settings.
Infoblox says this is the first publicly reported case of abusing DNS CNAMEs for TDS, although most likely not the first time it happened, so they decided to name the method 'CNAME TDS.'
"Savvy Seahorse is the first publicly reported threat actor abusing DNS CNAMEs as part of a malicious TDS," explains Infoblox.
"While it requires more sophistication in DNS on the part of the threat actor, it is not uncommon—just unrecognized up to this point in the security literature."
Using domain generation algorithms (DGAs), Savvy Seahorse creates and manages thousands of domains utilized in the CNAME TDS system.
The threat actor uses wildcard DNS responses to change the status of these domains from "parked," "in testing," and in "active campaign," making tracking and mapping of its infrastructure harder.
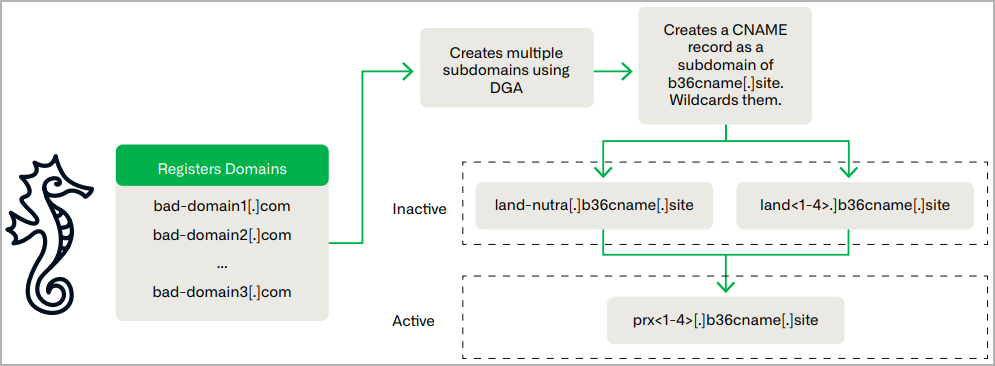
Also, unlike most threat actors, Savvy Seahorse spreads its infrastructure across multiple registrars and hosting providers, which helps both evade attribution and achieve operational resilience.
Campaign details
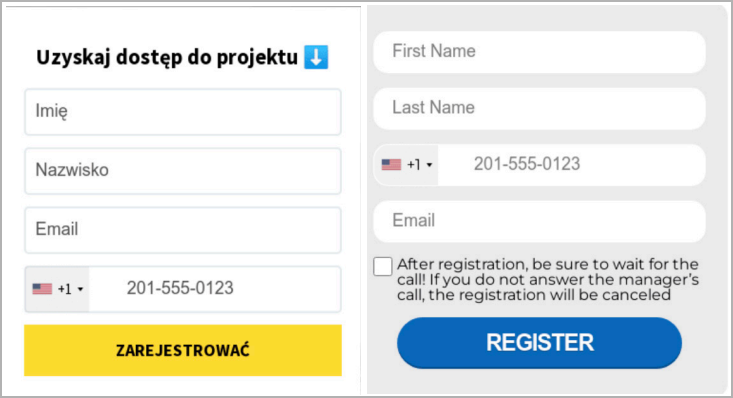
Savvy Seahorse promotes investment scams with lures written in English, Russian, Polish, Italian, German, French, Spanish, Czech, and Turkish, indicating the threat actor's global targeting scope.
The malicious subdomains used in the attacks host registration forms designed to steal the personal information of the tricked victims.
Once that data is submitted, a secondary domain validates the victim's location based on their IP address and the legitimacy of the provided info and redirects approved users to a fake trading platform.
There, victims can choose to top up their investment balances using credit cards, cryptocurrency, and other payment methods.
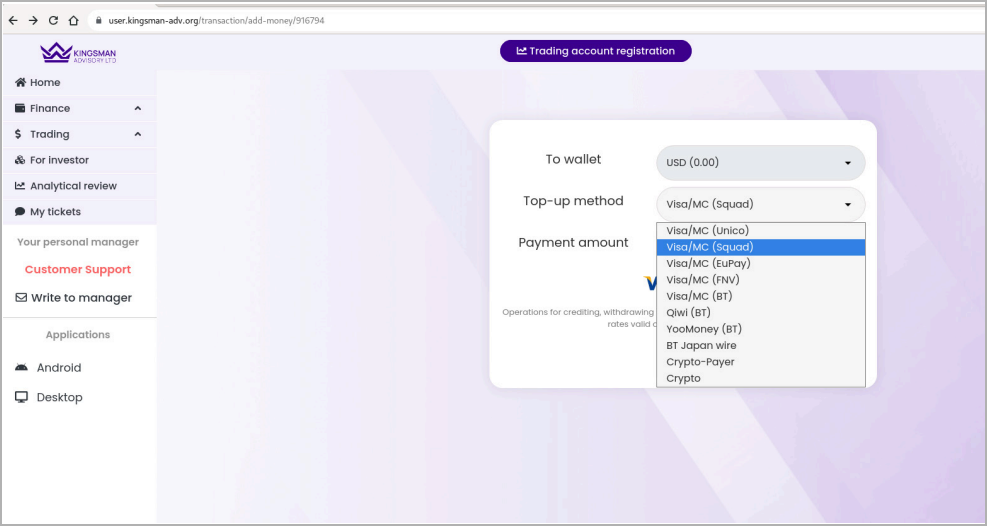
The following video demonstrates one of these fraudulent platforms in detail:
Chatbots impersonating ChatGPT, WhatsApp, and Tesla, among other well-known entities, increase the apparent legitimacy and play a vital role in the social engineering aspect of the attack.
Infoblox says the malicious pages also use Meta Pixel trackers for performance tracking, which is likely used to refine tactics.
For a complete list of indicators of compromise and domains used in Savvy Seahorse campaigns, check out this GitHub page.


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now