Today a new Locky Ransomware variant was discovered by security researcher Derek Knight and then quickly followed by Stormshield malware analyst coldshell that switches to the .ykcol extension for encrypted files. For those who may not have noticed it the first time, like myself, ykcol is locky spelled backwards.
It is important to note that if you are infected with this ransomware, you are not infected with the Ykcol Ransomware, as some sites may call it. You are instead infected by Locky, which is using the .ykcol extension.
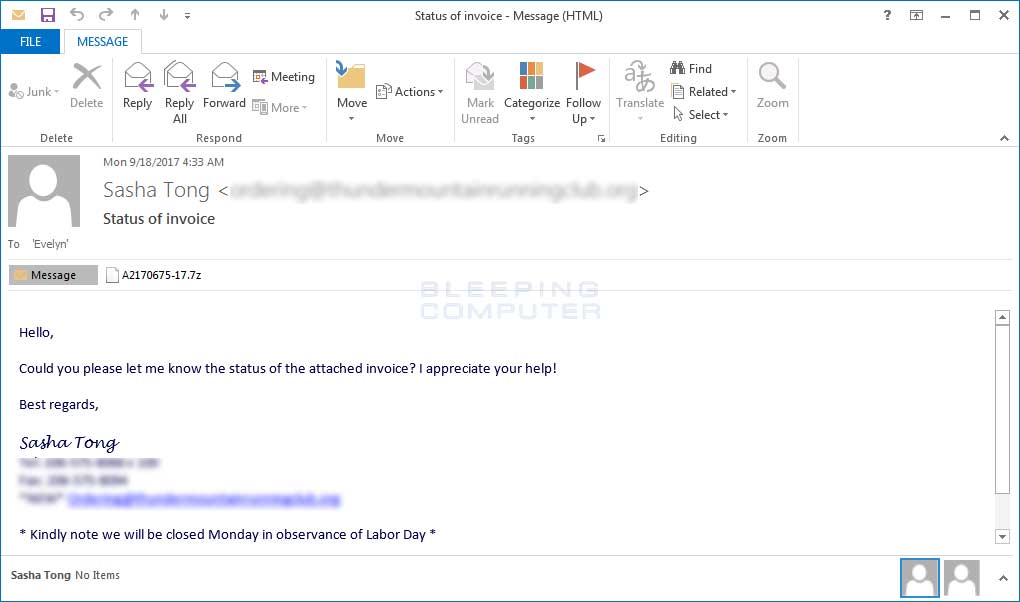
This variant is currently being distributed via spam emails that have a subject line of Status of invoice, which contain a 7zip, or 7z, attachment. This attachment contains a VBS file, which when executed will download the Locky executable from a remote site and execute it.
It is strange that they are using a 7z attachment considering that many recipients may not have the software required to open it. This is probably being done to bypass more stringent filters put in place recently by Gmail and other mail services.
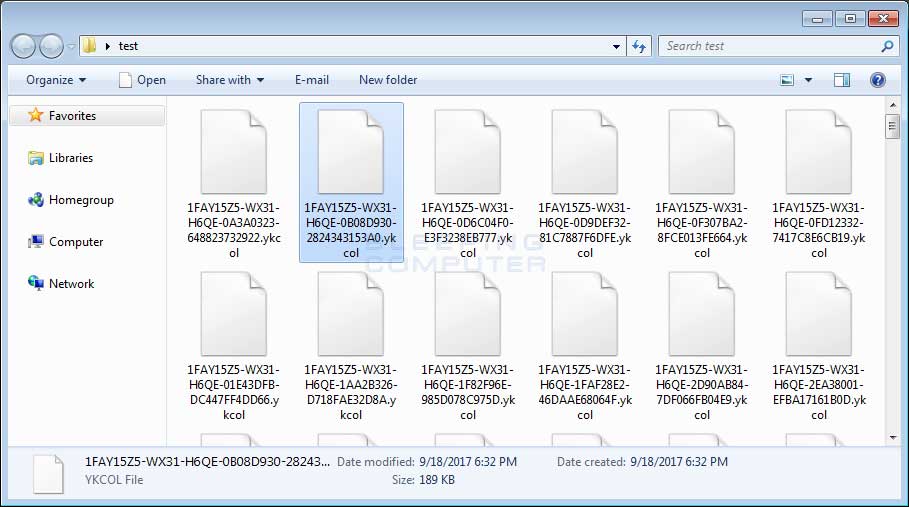
Once the file is downloaded and executed, it will scan the computer for files and encrypt them. When this Locky variant encrypts a file it will modify the file name and then append the .ykcol. When renaming the file, it uses the format [first_8_hexadecimal_chars_of_id]-[next_4_hexadecimal_chars_of_id]-[next_4_hexadecimal_chars_of_id]-[4_hexadecimal_chars]-[12_hexadecimal_chars].ykcol.
This means that a file named 1.png would be encrypted and named something like as E87091F1-D24A-922B-00F6B112-72BB7EA6EADF.ykcol.
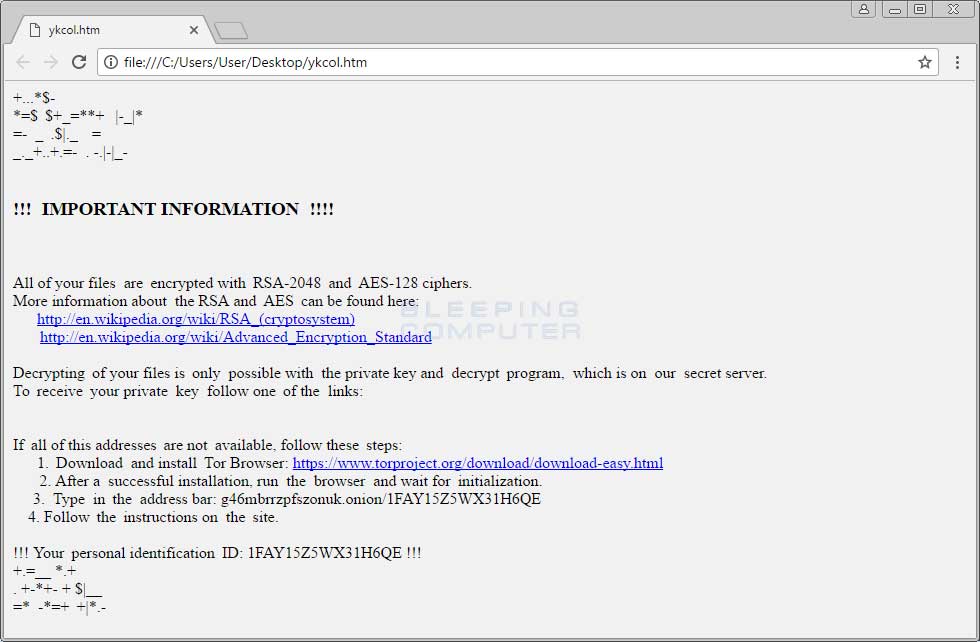
When Locky has finished encrypting the computer, it will remove the downloaded executable and then display a ransom note that provides information on how to pay the ransom. The names of these ransom notes have changed for this version to ykcol.htm and ykcol.bmp.
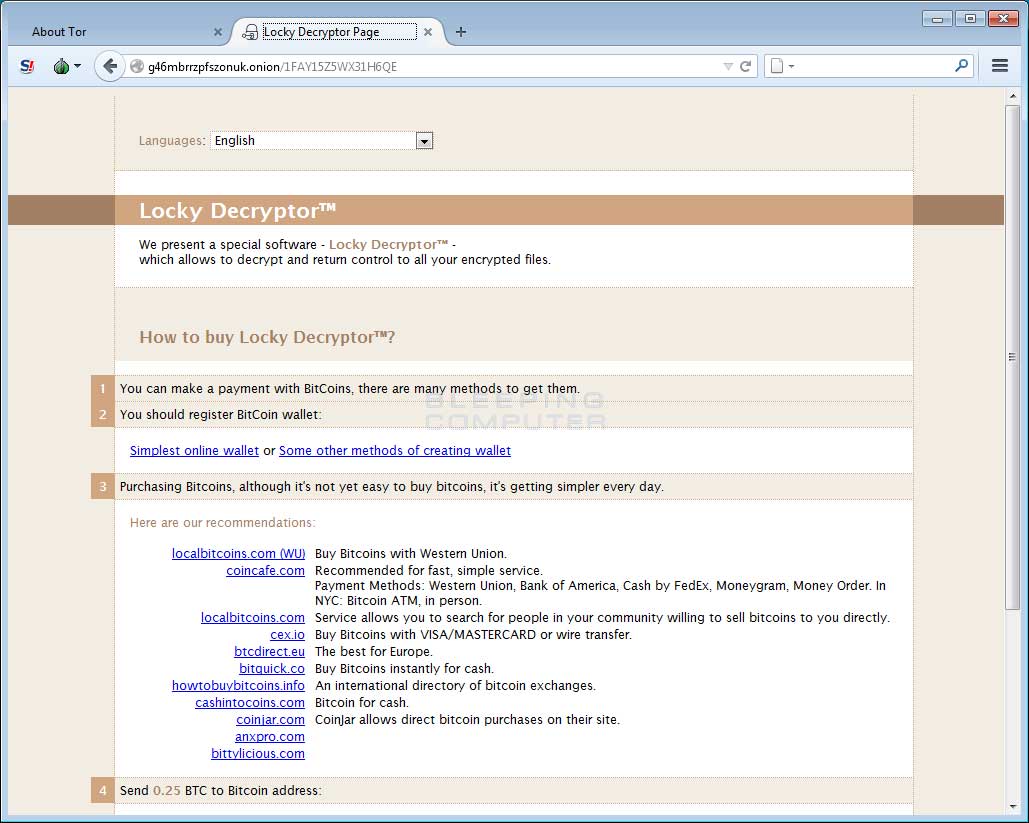
At the time of this writing, the Locky Decryptor TOR payment site has the ransom set to .25 BTC or approximately $1.025 USD.
It is not possible to decrypt the Locky Ransomware Ykcol Variant
Unfortunately, at this time it is still not possible to decrypt .ykcol files encrypted by the Locky Ransomware for free.
The only way to recover encrypted files is via a backup, or if you are incredibly lucky, through Shadow Volume Copies. Though Locky does attempt to remove Shadow Volume Copies, in rare cases ransomware infections fail to do so for whatever reason. Due to this, if you do not have a viable backup, I always suggest people try as a last resort to restore encrypted files from Shadow Volume Copies as well.
For those who wish to discuss the Locky ransomware or need support, you can use our dedicated Locky Ransomware Help & Support Topic.
How to protect yourself from the Locky Ransomware
In order to protect yourself from Locky, or from any ransomware, it is important that you use good computing habits and security software. First and foremost, you should always have a reliable and tested backup of your data that can be restored in the case of an emergency, such as a ransomware attack.
You should also have security software that contains behavioral detections such as Emsisoft Anti-Malware or Malwarebytes.
Last, but not least, make sure you practice the following good online security habits, which in many cases are the most important steps of all:
- Backup, Backup, Backup!
- Do not open attachments if you do not know who sent them.
- Do not open attachments until you confirm that the person actually sent you them,
- Scan attachments with tools like VirusTotal.
- Make sure all Windows updates are installed as soon as they come out! Also make sure you update all programs, especially Java, Flash, and Adobe Reader. Older programs contain security vulnerabilities that are commonly exploited by malware distributors. Therefore it is important to keep them updated.
- Make sure you use have some sort of security software installed.
- Use hard passwords and never reuse the same password at multiple sites.
For a complete guide on ransomware protection, you visit our How to Protect and Harden a Computer against Ransomware article.
IOCs
Hash:
SHA256: c674da5f1c063a0bec896d03492620ac94687e7687a1b91944d93c1d6527c8a7


Post a Comment Community Rules
You need to login in order to post a comment
Not a member yet? Register Now